Ryan Trost, co-founder and chief technical officer, ThreatQuotient, has highlighted three premonitions for 2020 and predicted that at least one high-value operational technology network get infiltrated and held for ransom
Companies continue to flock to cloud deployments, both private and public, to regain budget and unburden their IT departments. Teams have slightly more control and oversight over private cloud deployments but the public multi-tenant cloud deployments are target-rich for an attacker. By studying how a single cloud technology operates from infrastructure to defences, adversaries become more efficient and significantly decrease their attack costs.
Most adversaries are driven by financial gains and a significant operating metric for them revolves around their operational costs. Very similar to our defensive budgets, adversaries must weigh their operating costs against their potential profits.
“Security teams must absolutely have a voice at the table when deciding ‘which’ cloud environment. Security teams must evaluate and scrutinise cloud security practices to ensure due diligence is being performed by the vendor - for instance, ensuring the cloud vendor is undergoing routine penetration tests and not only resolving any weaknesses identified but how quickly is their security team identifying the penetration test.”
A staggering surge of botnet armies
Botnet armies are nothing new, however, as endpoint devices in households become “connected” and schools provide each individual student with personal computing devices it opens the doors for widespread takeover.
“I can appreciate the benefits of every single student having a tablet (or equivalent) for schooling. However, I struggle to find the legitimacy of why my refrigerator needs an Internet connection, or for that matter, a video conferencing feature. As with any botnet army, the individual devices don’t hold any real threat value but when controlled in the masses they provide a formidable attack mechanism for cybercriminals.”
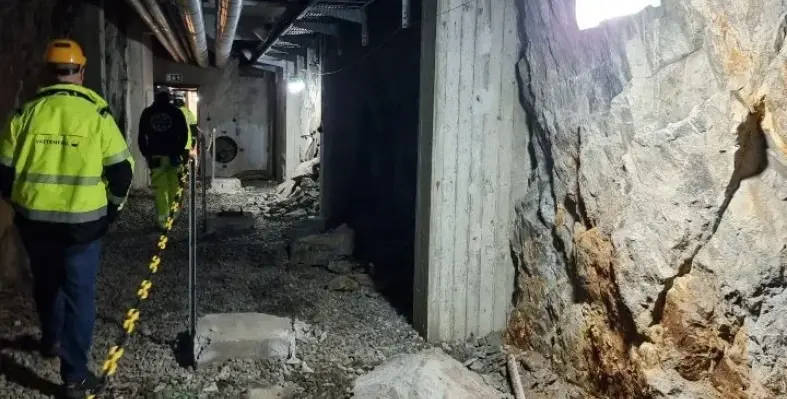
Operational technology line to fall victim to a ransomware threat
Operational technology (OT) networks are the primary life source for oil, gas and energy companies, as well as, massive manufacturing industries such as automotive. These environments typically rely heavily on older infrastructure and technology and are infrequently updated to the latest security levels.
Oftentimes, OT networks are overlooked because they don’t have the traditional weak points most organisations are defending for two primary reasons
1. They generally are not connected to the Internet
2. They do not have a high number of end-users who are susceptible to crafty email spear phish attacks or ‘click-happy’ websurfing.
But as manufacturers live and die by product branding the importance for a company to comply with criminal demands warrants a lofty ransom threat. According to Trost, 2020 will see at least one high-value OT network get infiltrated and held for ransom.