Security
Security
- Details
- Kestell Duxbury
- Security
- Topic: Security
- Date: 25 September, 2017
- Year: 2017
ABM is to promote and distribute Ring’s home security products and solutions through its strong partner network across the region
Ring, the leader in home security, has announced that it has signed a value-added distribution (VAD) agreement with Arab Business Machine Middle East (ABM) for the Middle East and North Africa (MENA). As per the agreement, ABM will promote and distribute Ring’s home security products and solutions and offer value-added services through its extensive channel partner network.
Ring is expanding its global presence and operations in response to the region witnessing a positive growth of the property sector with many developers focusing on building master-planned communities and the increasing demand for home security solutions.
ABM will distribute Ring’s best-of-breed home security solutions in the UAE, Jordan, Lebanon, Oman, Kuwait, Qatar, Bahrain, Egypt, Algeria, Tunisia, Morocco and Iraq.
“Your home is not an asset – your home is a place that has much more meaning to it and it is something you want to protect and also monitor. Ring believes in keeping homes and communities safe rather than just comfortable and we hope to change the way homeowners view security by keeping an eye on their family and property, even when they cant. Ring re-imagined the doorbell so consumers could respond – using a smartphone – to someone at their front door from anyplace, anytime while simplifying the technology with the combination of App, Cloud and Security hardware. ABM is very well placed in the MENA region to position our smart home security products with its broader reach across key retailers, Internet Service Providers and online stores. ABM’s experience in selling Apple products for more than a decade gives us the further confidence of its capabilities on best in class retail execution for Ring’s range of the products and solutions,” says Mohammad Meraj Hoda, Managing Director of Ring.
Ring has evolved as the leading brand in the Smart Home Security Space represented by 16000 plus stores across North America and Ring’s products globally have been hailed as a dependable second set of eyes and ears to deter would-be thieves from entering homes and communities. It has been proven that Ring doorbells can reduce crime by up to 55 per cent in neighbourhoods, and the goal is to bring the same convenience and security to the Middle East neighbourhoods.
As the VAD, ABM will distribute Ring’s latest suite of smart home security products such as Ring Video Doorbell, Ring Video Doorbell Pro, Video Doorbell Elite, Ring Floodlight Cam and the new Ring Spotlight Cam and conduct channel engagement, training and activation programs for partners. ABM will also set up go-to-market strategies with key retail partners and provide the needed infrastructure for micro-channel to engage with the Ring brand.
“We are continuously evaluating new and innovative technologies and emerging trends to add to our portfolio, which have a direct impact on the dynamics of the home security industry in the residential security sector in the MENA region. This makes our partnership with Ring a perfect fit. We see exciting new possibilities in this partnership with Ring across the MENA region and it will help ABM to better address our customer’s needs in today’s environment of ever-increasing demand for home security solutions,” said Ghassan Bendali, General Manager of ABM Middle East.
- Details
- Kestell Duxbury
- Security
- Topic: Security
- Date: 21 September, 2017
- Year: 2017
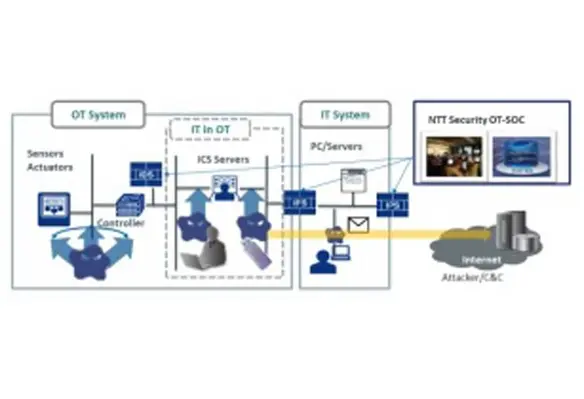
NTT Security Corporation, the specialised security company of NTT Group, has launched “IT/OT Integrated Security Services”
- Details
- Deblina Roy
- Security
- Topic: Security
- Date: 20 September, 2017
- Year: 2017
Ievo Ltd, the Newcastle-based manufacturer of fingerprint biometric solution, has appointed Network Information Technology (NIT) as a new distribution partner for its biometric recognition products in the Middle East, Turkey and Africa (META) region
- Details
- Deblina Roy
- Security
- Topic: Security
- Date: 11 September, 2017
- Year: 2017
DNV GL’s new DNVGL-RP-G108 cyber security aims to help the operators, system integrators and vendors to manage and prevent emerging cyber threat in the oil and gas industry, which is caused due to the increased digitalisation in the sector across the world
- Details
- Kestell Duxbury
- Security
- Topic: Security
- Date: 10 September, 2017
- Year: 2017
The global malware attack that affected more than 200,000 organisations in 150 countries has brought cyber crime to the top of the risk news agenda
Wanna Decryptor, also known as WannaCry, started taking over people’s computers on 12 May 2017, demanding payments of US$300 to restore access to the files it encrypted. It threatened to delete files within seven days if no payment was made, and threw the UKs National Health Service into chaos.
While it is difficult to prevent determined, well-resourced hackers from launching a technical attack on a network, the truth is that most ransomware attacks generally rely on an interaction with our own users, says Mike Gillespie, IIRSMs Cyber Security Expert and Director of security consultancy Advent IM.
“Cyber attackers usually need to download the malicious software onto a computer, phone or other connected device, including – in the case of the NHS – such things as medical imaging devices and laboratory analysers to name a few, combined with many organisations failing to apply appropriate system and security patches. This combination effectively presents a much more vulnerable environment to the potential attackers, yet without organisations fully understanding the inherent risk.”
The most common ways of installing malware – malicious software – which includes the ever growing family of ransomwares, are through compromised emails and websites. For example, hackers could send an employee a phishing email that looks like it comes from their boss asking them to open a link – but it actually links to a malicious website that surreptitiously downloads the malware onto their computer.
The WannaCry ransomware appears to have used a flaw in Microsofts software, discovered by the National Security Agency and leaked by hackers, to spread rapidly across networks locking away files. While the exact means of delivering the payload is not yet known, WannnaCry is especially interesting for the manner in which it spread, acting more like a worm than most other ransomware does.
A security expert managed to stop the attack by triggering a kill switch about 24 hours later but it continued to wreak havoc, with a second variant being released hot on the heels of the original one.
“All organisations need to become much more familiar with threat and vulnerability, two key components of risk,” adds Mike. “There is a growing need to fully understand the increased connectivity of everything, the convergence of physical and cyber threat and the significant vulnerability that under-aware staff can introduce. Cyber security is no longer in its own silo, but rather it is all-pervasive and affects almost everything we touch and interact with.”
It is time for organisations to realise that the threat is holistic, and so too must be the defence, Mike concludes.
Risk Reducing tips from IIRSMs cyber security expert:
- Educate all staff ... this includes senior management. Education should be targeted, pertinent, interesting, ongoing and effective.
- Make information asset ownership an integral part of all senior management roles.
- Protect especially sensitive information assets as identified by Information Asset Officers more rigorously, using a range of blended technical defences including network access controls, protective monmitoring and regularly updated anti-malware software.
- Implement an effective and risk based backup strategy to ensure that all vital information assets can be recovered in the event of a compromise. This should be an integral part of your business continuity, resilience and forensic readiness planning.
- Never, ever pay a ransom.